Software patches are concise, targeted updates released by software vendors to fix vulnerabilities, address bugs, and sometimes improve performance. They form a critical line of defense and a core element of patch management strategies that balance risk with uptime. While we often hear about fixes for security holes, these updates also enhance reliability and efficiency by resolving known flaws and compatibility issues. In this brief overview, you’ll learn what patches are, why they matter for security and performance, and how to manage them effectively. A disciplined approach to patching helps organizations reduce risk while keeping systems productive.
Beyond the label, these maintenance releases are best viewed as deliberate measures to close gaps, strengthen defenses, and stabilize operations. This ongoing effort aligns with vulnerability remediation concepts, emphasizing planning, testing, and governance to minimize disruption. In practice, teams describe update cycles, change control, and pilot deployments to ensure new code improves security and performance without surprising users. Framing patches as a proactive, disciplined practice helps organizations build resilient IT environments that adapt to evolving threats.
Understanding Software patches and their role in security and performance
Software patches are small, targeted updates released by vendors to fix vulnerabilities, address bugs, and occasionally enhance functionality. They are a core element of patch management and software updates, designed to close security gaps while improving reliability and efficiency. By promptly applying patches, organizations reduce exposure to threats and keep systems aligned with current best practices for security and performance.
While many patches address security vulnerabilities (security patches), they can also deliver stability improvements and feature refinements. This dual benefit underscores the importance of robust patching best practices and a proactive vulnerability remediation approach. Treating patches as part of an ongoing security and maintenance strategy helps balance risk reduction with operational productivity.
The patch management lifecycle: from inventory to rollback
The patch management lifecycle encompasses identifying, testing, deploying, and verifying patches across an organization. A well-defined lifecycle reduces security exposure while minimizing disruption to services. Core activities include inventory and assessment, which establish what needs patching and the risk profile of each update.
Subsequent stages—prioritization, testing in a staging environment, controlled deployment, verification, and rollback planning—ensure patches are applied safely. This lifecycle is central to effective patch management, aligning vulnerability remediation with business needs and maintaining governance over change management.
Security patches and vulnerability remediation: prioritization and testing
Security patches are the most critical updates for closing known flaws and reducing the chance of exploitation. Timely application is essential to shrink the window of vulnerability and support vulnerability remediation efforts. Integrating vulnerability management with patch management helps identify which patches address the most severe risks and highest exposure.
Testing remains a cornerstone of successful remediation. By validating patches in staging environments and using risk-based prioritization, organizations avoid introducing compatibility issues while still delivering essential security updates. This approach also addresses regulatory expectations for timely and verifiable patching.
Patching best practices for robust defensive postures
Patching best practices combine people, processes, and technology to create a resilient update program. Key elements include an up-to-date asset inventory, risk-based prioritization, and automated scanning, downloading, and deployment. Establishing clear change control records helps maintain accountability across patching activities.
Additional practices include testing patches before broad rollout, scheduling maintenance windows to minimize disruption, implementing phased deployments, and preparing rollback plans. Ongoing monitoring and documentation ensure issues are detected early and that governance remains aligned with organizational security objectives.
Deployment strategies: phased rollout, maintenance windows, and automation
Deployment strategies aim to minimize downtime and risk by using phased rollouts, pilot groups, and well-defined maintenance windows. This approach allows teams to observe behavior in controlled segments before broader distribution, reducing the impact of unexpected patch interactions.
Automation plays a critical role in executing consistent software updates across endpoints and servers. Tools such as endpoint management platforms, centralized patch catalogs, and vulnerability management integrations streamline the process, while change management alignment ensures approvals and outcomes are well documented.
Beyond security: how software updates boost reliability and performance
Software updates often fix bugs that affect reliability, memory management, and performance. By addressing these defects, patches can reduce downtime and improve system responsiveness, contributing to a smoother user experience and more stable operations.
Regular, disciplined patching supports long-term IT health by maintaining compatibility with newer hardware and software, meeting compliance requirements, and strengthening security posture. Emphasizing a holistic patching program—focused on patch management, software updates, and ongoing vulnerability remediation—helps organizations sustain productive and secure environments.
Frequently Asked Questions
What distinguishes software patches from other software updates in patch management?
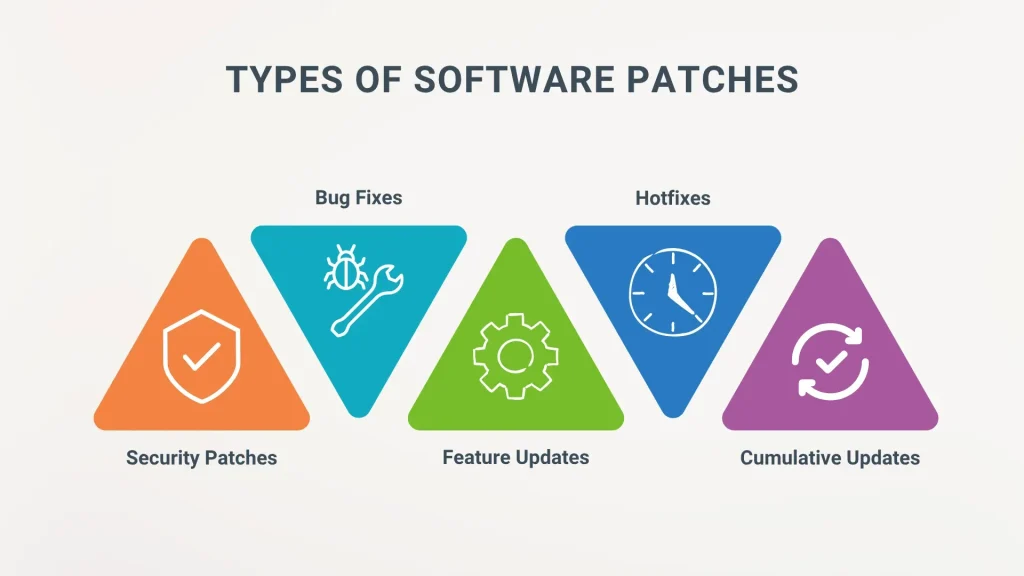
Software patches are targeted fixes that address vulnerabilities, repair bugs, and often improve stability, whereas general software updates may add features or performance tweaks. In patch management, classify patches as security patches, bug fixes, or feature/ cumulative patches, and follow testing and staged deployment to minimize risk while applying vulnerability remediation.
Why should security patches be prioritized within patch management?
Security patches fix known vulnerabilities, reduce the attack surface, protect sensitive data, and support regulatory compliance. Prioritizing security patches in risk-based prioritization helps shorten remediation windows and lowers overall risk.
How do software updates relate to vulnerability remediation through patches?
Software updates often include patches; vulnerability remediation is achieved by applying security patches promptly, ideally after testing in a staging environment. Use patch management practices like phased rollout and verification to avoid disruption.
What is the patch management lifecycle and where do software updates fit in?
The lifecycle includes inventory and assessment, prioritization, testing in staging, deployment, verification and reporting, and rollback planning. Software updates are part of the broader patching activity, while security patches receive higher priority in testing and deployment.
What are best practices for patching to minimize risk and disruption?
Maintain an up-to-date asset inventory; use risk-based prioritization; test patches in a controlled environment; automate scanning, downloading, and deployment; schedule maintenance windows; implement phased rollouts; verify post-deployment and maintain rollback plans; document procedures.
How should organizations handle emergency patches or hotfixes?
Emergency patches (hotfixes) require immediate attention, but should still follow patch management checks: assess risk, apply in a controlled manner when possible, monitor for issues, and have rollback options. Then complete full testing later and update change records.
| Topic | Summary |
|---|---|
| What are software patches? | Code updates that fix flaws, close security holes, or improve functionality. They can be small or large and cover operating systems, applications, databases, and firmware. Forms include security patches, bug fixes, and cumulative/feature patches. |
| Patch management lifecycle | Process of identifying, testing, deploying, and verifying patches. Core stages: inventory and assessment, prioritization, testing in staging, deployment, verification and reporting, rollback planning. |
| Why patches matter for security | Security patches reduce vulnerability exposure, protect sensitive data, and help meet regulatory requirements by closing exploitable gaps. |
| Security patches vs. other updates | Not all updates are security patches, but security patches are high priority. Balance speed with testing; hotfixes may follow by thorough updates. |
| Patches for performance and reliability | Patches can fix bugs, optimize code, reduce downtime, and improve system responsiveness and user experience. |
| Risk of delaying patches | Delays increase chances of exploits, compliance penalties, operational issues, and higher remediation costs. |
| Best practices for patch management | Maintain inventory, prioritize by risk, test in controlled environments, automate where possible, schedule maintenance windows, use phased rollout, verify and monitor, prepare rollback plans. |
| Tools and approaches for patch management | Endpoint management platforms, centralized patch catalogs, vulnerability management integrations, change management alignment, and cloud/on-premises patching strategies. |
| Common obstacles and how to overcome them | Compatibility issues, interdependencies, and downtime constraints. Overcome with testing, staged deployments with rollback, vendor updates, and clear documentation. |
| Practical patching plan | Inventory assets and risk, map patch types to risk, establish production-like testing, schedule rolling deployments, automate where possible, monitor outcomes, review quarterly. |