Patch management is the disciplined process of identifying, acquiring, testing, deploying, and verifying patches across an organization’s hardware and software estate. Following patch management best practices, organizations should recognize the importance of patches, emphasize vulnerability patch management, and pursue automated patching and thoughtful patch deployment strategies. This approach reduces exposure to known vulnerabilities and supports reliability across operating systems, applications, and cloud services, including mobile devices and virtual environments. Yet many teams face scale, complexity, third-party software, and the speed of threats, which requires pragmatic planning, phased migrations, and clear accountability. This article explains why patches matter for security and stability and how to implement effective patching practices.
In other terms, the topic can be framed as vulnerability remediation and software updates, where systems stay current to reduce risk. Many organizations implement automated patching, continuous monitoring, and defined patch deployment strategies to minimize exposure and downtime. From a risk-management perspective, prioritizing security fixes, validating compatibility, and documenting changes are central to a resilient update program. Ultimately, the goal is to maintain trust in IT services while avoiding disruption through careful planning and executive sponsorship.
Patch Management: The Essential Role in Modern Cybersecurity
Patch management is the disciplined process of identifying, acquiring, testing, deploying, and verifying patches across an organization’s hardware and software estate. Patches fix vulnerabilities, close security gaps, and improve stability by addressing bugs that could cause crashes or performance degradation. The importance of patches lies in reducing exposure to known vulnerabilities before attackers exploit them. This aligns with patch management best practices to create a repeatable, auditable lifecycle for remediation, governance, and risk reduction.
Effective patch management reduces attack surface, helps with regulatory compliance, and supports a more predictable IT environment. It’s not just about security; patches often fix stability issues and compatibility problems that can otherwise lead to outages, degraded performance, or unhappy users. By following a structured approach to patching, organizations strengthen vulnerability patch management and demonstrate diligence to stakeholders and regulators.
Achieving System Stability Through Patch Management
Stability is a core driver for patching; patching speed must be balanced with caution. Inconsistent patching creates mixed versions causing crashes and unpredictable behavior after updates. Incorporating patch deployment strategies such as phased rollouts and maintenance windows can preserve service levels while still addressing critical fixes. Automated patching can help enforce consistent timing and reduce human error, especially across large fleets.
By aligning patching with change management and rollback plans, organizations minimize downtime and disruptions. Clear communication and testing in staging environments support reliability. Automated patching should be configured with safeguards such as pre-deployment checks, backup, and rollback triggers to protect uptime.
The Patch Management Lifecycle: From Inventory to Verification
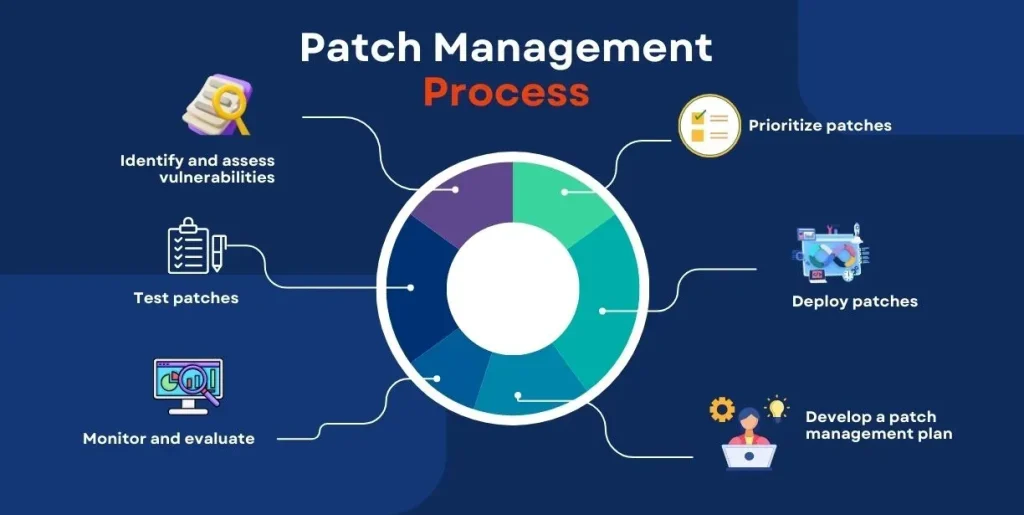
An end-to-end lifecycle begins with inventory, mapping hardware, OS, applications, and firmware to establish visibility. A vulnerability assessment identifies patches, their severity, and potential impact on security and operations. Prioritization uses risk scoring to decide what to apply first, with critical security patches taking precedence for fast deployment. This frame aligns with vulnerability patch management concepts.
Testing and staging verify compatibility and performance before broad deployment, followed by systematic deployment and post-deployment verification. Documentation and auditing capture actions, outcomes, and timelines to support compliance and continual improvement, and they help inform patch deployment strategies across teams.
Best Practices for Patch Management in Complex Environments
Asset inventory, clear policy, and risk-based prioritization are foundational. Align with patch management best practices: maintain complete asset inventory, define roles, establish maintenance windows, and implement rollback procedures.
Automation plays a central role, with scheduled deployments, automated scanning, verification, and reporting. Separate production and test environments; maintain a robust rollback plan; logs and audits help demonstrate compliance. This approach supports vulnerability patch management by ensuring consistent, auditable remediation across the enterprise.
Automating Patch Management: Tools, Approaches, and Strategies
Automation reduces manual effort and accelerates remediation. Tools like Windows Update Services (WSUS), System Center Configuration Manager (SCCM), and other patch management platforms enable automated patching, vulnerability scanning, and reporting. Cloud-native patching and vulnerability scanners complement posture across OS, apps, and cloud workloads. Patch deployment strategies such as phased rollouts and pilots minimize risk while delivering timely fixes.
Consider agent-based vs agentless approaches; each has tradeoffs in visibility, control, and footprint. A balanced automation strategy combines policy-driven scheduling, testing in staging, and robust rollback capabilities to protect service continuity. By embedding automated patching into the workflow, organizations can more reliably apply critical updates without interrupting essential services.
Measuring Success and Ensuring Compliance in Patch Management
Metrics matter: patch coverage, time-to-patch, and success rate indicate how well patches are applied and maintained. The importance of patches is reinforced by dashboards, reports, and audit trails that demonstrate vulnerability patch management progress and regulatory alignment.
Continuously improve by reviewing outcomes, refining risk scoring, updating playbooks, and documenting actions. Compliance programs benefit from centralized evidence of remediation, change controls, and policy enforcement, closing gaps and driving maturity in patch management.
Frequently Asked Questions
What is patch management and how do patch management best practices improve security and stability?
Patch management is the disciplined lifecycle of identifying, acquiring, testing, deploying, and verifying patches across an organization’s assets. Following patch management best practices—inventory, risk-based prioritization, staging/testing, automated deployment, verification, and auditing—reduces exposure to known vulnerabilities, minimizes outages, and improves overall system stability.
Why is the importance of patches critical to security, and how does patch management address it?
Patches fix security gaps and address defects that attackers could exploit. In patch management, prioritizing critical security patches and applying them promptly reduces the attack surface, supports regulatory compliance, and helps maintain trusted endpoints, servers, and services.
How does vulnerability patch management fit into a broader patch management strategy?
Vulnerability patch management focuses on identifying and prioritizing patches by risk. Integrated into the full patch management lifecycle, it guides testing, staged deployment, and verification to ensure patches resolve vulnerabilities without disrupting operations.
What role does automated patching play in modern patch management and deployment?
Automated patching speeds detection, testing, and rollout. By automating scanning, prioritization, deployment, and post-install verification, you reduce manual errors, shorten remediation times, and maintain consistent patch hygiene across operating systems, applications, and devices.
What patch deployment strategies work best for large organizations?
Effective patch deployment strategies use phased rollouts, pilot groups, and staged deployments aligned with maintenance windows. Combine centralized control with region-specific pilots, rapid rollback plans, and clear communication to minimize risk and downtime.
How can I measure patch management success and demonstrate a mature program?
Track metrics such as patch compliance rate, mean time to patch, time to remediation, and audit-ready documentation. Regular verification, testing outcomes, and centralized dashboards help demonstrate risk reduction, regulatory alignment, and continuous improvement in patch management.
| Topic | Key Points |
|---|---|
| Definition of Patch Management | A disciplined process to identify, acquire, test, deploy, and verify patches across hardware and software to fix vulnerabilities and improve stability. |
| Scope and Coverage | Covers operating systems, installed applications, firmware, network devices, and extends to cloud services and containers. |
| Patch Management Lifecycle (Key Stages) | Inventory → Vulnerability assessment → Prioritization → Testing/Staging → Deployment → Verification → Documentation/Auditing. |
| Why It Matters for Security | Reduces attack surface, supports regulatory compliance, and helps prevent malware, ransomware, and data breaches. |
| Patch Management and Stability | Balances speed with caution; testing and maintenance windows, plus rollback plans, minimize outages and maintain reliability. |
| Best Practices | Asset inventory, policy with roles, risk-based prioritization, pre-deployment testing, automation, strategic scheduling, post-patch verification, rollback planning, and audit logging. |
| Tools & Automation | OS patching tools (e.g., WSUS, SCCM, Windows Update for Business, yum/dnf, apt); third-party patching; patch management platforms (Qualys, Ivanti, ManageEngine, Tenable); cloud-native patches; agent-based vs agentless approaches; phased rollout strategies. |
| Challenges | Scale and complexity, third-party/legacy software gaps, compatibility and regression risk, patch fatigue, and compliance demands. |
| Real-World Perspective | Case study shows improved security posture, fewer outages, and better reliability when a defined lifecycle, testing, and cross-team communication are in place. |