Software patch management is a critical discipline in modern IT operations. It covers the people, processes, and technology needed to identify, test, and apply updates across operating systems, applications, and firmware. In a world where cyber threats surface daily, a solid patching strategy helps reduce risk and protect critical assets. A well-defined approach also minimizes downtime and supports regulatory compliance. This introductory guide outlines core concepts, practical steps, and best practices to help you build a resilient patching program.
From a terminology perspective, organizations talk about patching as part of an update lifecycle, focusing on timely fixes, tested deployments, and change governance. In practice, teams pursue vulnerability management and risk reduction by aligning detection, assessment, acquisition, testing, and rollout of fixes. This framing aligns with modern devops and security practices by prioritizing early detection and controlled change. For organizations, the goal is a repeatable, auditable process that scales with growth and cloud adoption. Using governance, automation, and clear ownership reduces the risk of patch gaps and ensures consistent updates. Ultimately, a mature approach blends risk-based decision making with user-centric considerations, so patches land smoothly without unnecessary disruption. In practice, teams map patching to the broader cybersecurity program, leveraging threat intel, vendor advisories, and compliance requirements. If you care about resilience, this perspective highlights how update cycles become a competitive advantage rather than a burden. Organizations can further improve outcomes by tracking patching metrics, conducting regular reviews, and aligning patching with risk appetite. Clear communication with stakeholders about planned updates helps minimize disruption and builds organizational trust. Automated tooling supports rapid discovery, testing, and deployment while preserving rollback options and an auditable trail. Finally, documenting policies and procedures ensures consistency across teams and strengthens ongoing improvement.
Software Patch Management Essentials: What It Is and Why It Matters
Software patch management is the ongoing lifecycle management of patches, updates, and security fixes for software assets. It goes beyond simply clicking update; it requires accurate asset inventories, vulnerability awareness, and carefully staged deployment to minimize risk and disruption.
Effective patching reduces the attack surface and helps meet compliance obligations. Following patch management best practices, organizations align vulnerability management, software update management, and change governance to orchestrate timely security patching across endpoints, servers, and applications.
The Patch Management Process Framework: Steps from Discovery to Verification
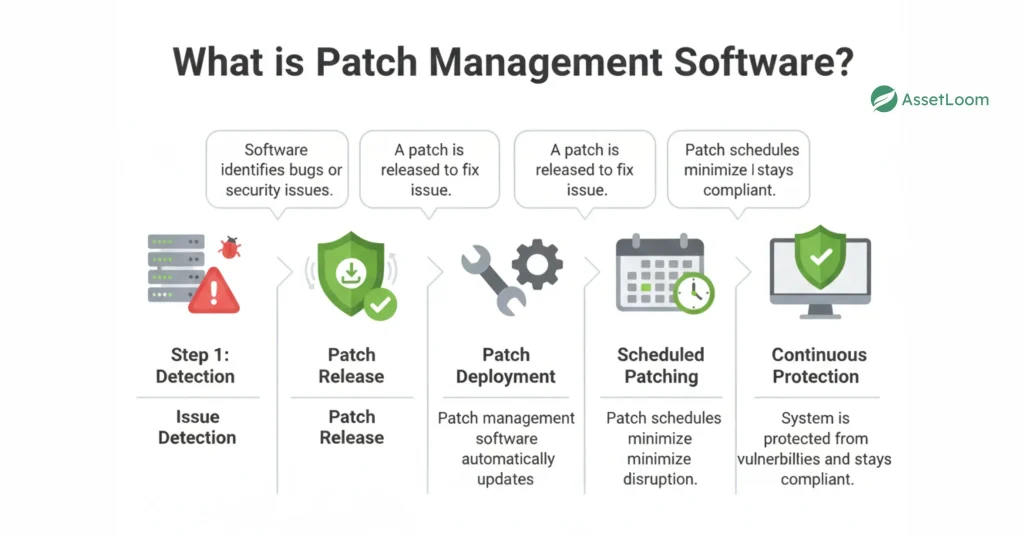
The patch management process begins with discovery and inventory of all software assets, followed by vulnerability assessment to identify exploitable weaknesses that patches can address. Patch acquisition relies on trusted sources to maintain integrity and authenticity.
Subsequent stages include testing and staging, deployment, verification, rollback planning, and documentation. Framing these steps as a repeatable process supports governance, auditability, and alignment with the patch management process.
Security Patching vs. Feature Patches: Balancing Risk and Innovation
Security patching prioritizes fixes for vulnerabilities that could be exploited by attackers, while feature patches add functionality or usability improvements. A balanced approach emphasizes security patching while monitoring potential regressions to maintain stability.
Adopting practices like phased rollouts and pilot deployments helps catch compatibility issues early, aligning with patch management best practices and vulnerability management objectives.
Tools, Roles, and Governance in Patch Management
A successful program relies on tools such as patch management software, WSUS, SCCM, and vulnerability management platforms that map patches to identified weaknesses. These tools enable software update management across on-premises and cloud environments.
Clear roles—IT administrators, security engineers, change management leads, and asset managers—coupled with a formal patch governance model, ensure consistent approvals, maintenance windows, and exception handling across teams.
Patch Deployment Strategies for Different Environments
Organizations commonly use strategies like phased rollout, maintenance window deployment, canary patches, and critical update blitz to balance speed and safety. Each approach reduces risk while accelerating remediation of exposed vulnerabilities.
Patch management must adapt to diverse environments—on-premises servers and endpoints, cloud assets, containers, and mobile devices—requiring tailored planning, monitoring, and rollback capabilities.
Measuring Success: Metrics, Compliance, and Continuous Improvement in Patch Management
Key metrics such as patch compliance rate, mean time to patch (MTTP), patch deployment success rate, and vulnerability remediation rate provide tangible visibility into program health and security posture.
Governance, audit trails, and ongoing evaluation underpin regulatory compliance and risk management, driving continuous improvement in patch management best practices.
Frequently Asked Questions
What is software patch management and why is it important?
Software patch management is the ongoing lifecycle of patches for software assets, from discovery to deployment. It matters because timely security patching closes vulnerabilities, reduces the attack surface, and helps meet compliance. In practice, it integrates with vulnerability management and software update management to balance security and stability.
What are the essential steps in the patch management process?
Core steps include discovery and inventory, vulnerability assessment, patch acquisition, testing and staging, deployment, verification, rollback planning, and documentation. Each phase supports vulnerability management and aligns with software update management, forming a repeatable patch management process for your organization.
How does security patching differ from feature patches, and why prioritize security patching in patch management?
Security patching focuses on fixing vulnerabilities to prevent exploits, while feature patches add new capabilities. In software patch management, security patching is prioritized based on risk and criticality, with testing and rollback designed to protect stability; balancing security patching with occasional feature updates is a core best practice in patch management.
What tools and roles are essential in a patch management program?
Essential tools include patch management software and vulnerability management platforms; for on-premises Windows environments, WSUS or SCCM can orchestrate updates, while cloud, containers, and mobile scenarios may rely on integrated patching solutions. Key roles include IT administrators, security engineers, change management leads, and asset managers, with a patch governance model guiding approvals and exceptions in patch management best practices.
How can organizations measure patch management success using key metrics?
Measure success with metrics such as Patch Compliance Rate, Mean Time to Patch (MTTP), Patch Deployment Success Rate, Vulnerability Remediation Rate, and Change Control effectiveness. Use dashboards and regular reporting to monitor the patch management program; these metrics reflect the effectiveness of vulnerability management and software update management within your patch management framework.
What are patch management best practices for hybrid environments (on‑premises, cloud, containers, and mobile)?
Common patch management best practices for hybrid environments include maintaining a complete asset inventory, prioritizing high-risk systems, automating discovery and deployment, using phased rollouts and maintenance windows, and applying canary patches. For containers, rebuild images and patch registries; for cloud, coordinate platform updates; for mobile, employ EMM/MDM controls. A unified patch management best practices approach helps ensure security patching and stability across all environments within the software patch management program.
| Aspect | Key Points |
|---|---|
| What is Software Patch Management | Ongoing lifecycle management of patches, updates, and security fixes across software assets. It is proactive (not just clicking update) and relies on asset inventories, vulnerability awareness, and staged deployment. The goal is to identify applicable patches, assess impact, validate no new issues, and deploy efficiently, often integrating vulnerability, change, and software update management to defend against threats. |
| Why Patch Management Matters | Closes security gaps, reduces attack surface, and lowers risk of malware, data breaches, and ransomware. Patches also fix bugs, improve performance, and improve compatibility, helping maintain service levels, minimize downtime, and support regulatory compliance. |
| Patch Management Process (Overview) | A repeatable lifecycle: discovery/inventory, vulnerability assessment, patch acquisition, testing/staging, deployment, verification, rollback planning, and documentation. |
| Discovery and Inventory | Build an up-to-date inventory of all software, operating systems, and firmware; automate discovery where possible to improve accuracy. |
| Vulnerability Assessment | Cross-reference inventory with vulnerability feeds and advisories to identify patches that address exploitable weaknesses; prioritize by risk and criticality. |
| Patch Acquisition | Retrieve patches from trusted sources; ensure patch integrity to avoid supply-chain risks. |
| Testing and Staging | Test patches in a controlled environment mirroring production to identify compatibility issues, performance impacts, and regressions; consider phased testing for critical systems. |
| Deployment | Roll patches out per a defined schedule and strategy (staged rollouts, maintenance windows, automated deployment) to minimize manual intervention and errors. |
| Verification | Confirm patches installed correctly and remain active; use post-deployment checks and health monitoring to verify success. |
| Rollback Planning | Prepare rollback procedures to revert quickly if a patch causes issues. |
| Documentation and Compliance | Record patch history, outcomes, and exceptions to support audits and measure effectiveness over time. |
| Tools, Roles, and Responsibilities | Use patch management software and vulnerability platforms; for on-premises Windows, WSUS or SCCM; integrate with cloud, endpoints, and config management tools. Roles include IT admins, security engineers, change managers, and asset managers; governance defines approvals, maintenance windows, and exceptions. |
| Patch Deployment Strategies | Adopt a mix: phased rollout, maintenance windows, canary patches, and rapid-but-controlled updates for critical vulnerabilities. |
| Security Patching vs. Feature Patches | Security patches fix vulnerabilities; feature patches add functionality. Prioritize security, but test for regressions and maintain balance with rollback plans. |
| Patch Management in Different Environments | Cover on‑premises, cloud, containers, and mobile/endpoint devices; each has unique challenges and coordination needs. |
| Measuring Patch Management Success | Track metrics like Patch Compliance Rate, Mean Time to Patch, Deployment Success Rate, Vulnerability Remediation Rate, and changes/incidents reductions. |
| Governance, Compliance, and Risk Management | Align with regulatory standards; document schedules, approvals, exceptions, and audit trails to demonstrate due diligence in vulnerability remediation. |
| Getting Started: Beginner Roadmap | Build asset inventory, define a patch policy, select integrating tools, establish production-like testing, implement staged rollouts, and create dashboards to monitor and improve patching. |
Summary
Software patch management is foundational to maintaining a secure, reliable, and compliant IT environment. By following a structured patching lifecycle—discovery, assessment, testing, deployment, verification, and governance—organizations reduce risk, shorten remediation times, and minimize downtime. With the right tools, clear roles, and a focus on security patching alongside ongoing vulnerability management, teams can demonstrate compliance and sustain trust in technology operations. A mature patch management program is ongoing, evolving with threats and changes in the IT landscape, and should start with visibility, governance, automation, and continuous measurement to maximize protection.