Patch management essentials are the backbone of a secure, reliable IT environment for small teams, guiding priorities, aligning IT with business goals, and reducing daily uncertainty. By embracing patch management best practices, you can reduce risk, shorten the exposure window, minimize downtime, and cultivate a culture of proactive maintenance that others can follow. This approach helps ensure patches are discovered, tested, and deployed in a predictable cycle, with clear ownership and minimal disruption to essential services. With clear roles, lightweight automation, governance, and practical change control, even a lean team can stay aligned with security goals while delivering measurable improvements. The result is fewer vulnerabilities, less downtime, and a more confident, resilient IT posture that supports growth, compliance, and customer trust.
Viewed through an LSI lens, the patching concept translates to vulnerability remediation, security updates, and ongoing software hygiene. Rather than a single event, it becomes an integrated lifecycle that begins with asset visibility and ends with verification and governance. Teams often describe this workflow as ongoing vulnerability management, cadence-driven update deployment, and proactive threat defense. By framing the practice this way, organizations of all sizes can recognize related activities such as patching, updates, and remediation as a shared security responsibility. The goal remains the same: reduce exploitable gaps, minimize disruption, and document outcomes for audit and improvement.
Patch management essentials: A practical starter for small teams
Patch management essentials form the backbone of a secure IT posture, particularly for small teams where resources are limited and downtime matters. Embracing patch management best practices and software update management helps reduce the window of vulnerability and keeps critical systems running smoothly. By focusing on vulnerability remediation as a core goal, teams can approach patching with clarity rather than chaos.
This beginner-friendly framing emphasizes a repeatable, scalable process that aligns security goals with business needs. It also sets expectations for patch management for small teams, ensuring that everyday operations can continue while security updates are applied in a controlled, auditable manner. Integrating cybersecurity patching into daily workflow helps teams stay ahead of threats without overwhelming staff.
Asset discovery and inventory as the foundation of patch management sustainability
Asset discovery and inventory anchor patch management by revealing what needs patching, on which devices, and when. Maintaining a current inventory supports patch management best practices and makes software update management practical in real-world environments.
Keeping an up-to-date inventory of devices, operating systems, applications, and versions enables precise patching, reduces redundant work, and provides a solid audit trail for vulnerability remediation. When inventory is accurate, patching decisions become data-driven and aligned with cybersecurity patching goals.
Risk-based patch identification and prioritization to maximize impact
Risk-based patch identification helps teams decide what to patch first by focusing on critical systems and known exploits. Prioritize patches by severity, likelihood of exploitation, and business impact, which echoes patch management best practices and vulnerability remediation principles.
By aligning patch choices with the real-world risk to the organization, teams can implement a pragmatic approach that balances speed and safety. This prioritization supports cybersecurity patching efforts and ensures resources are directed to the most significant threats.
Testing, staging, and safe deployment practices for small teams
Testing patches in a controlled environment minimizes surprises in production. In a small-team setting, designate a staging group or a subset of devices to validate patch impact on key apps and workflows, following a risk-based testing approach.
If full staging isn’t feasible, implement lighter testing focused on high-value assets and critical applications. This practice supports patch management for small teams, reduces the chance of downtime, and aligns with patch management best practices for safe deployment.
Automation and governance to sustain patch management essentials
Automation accelerates patch scanning, deployment, and reporting, helping limited staff keep pace with releases. Use lightweight automation to enforce consistent workflows while preserving control through approvals and rollback safeguards, aligning with software update management practices.
Establish governance, clearly defined roles, and change-control processes to maintain auditable records. Lean governance supports patch management best practices and ensures that cybersecurity patching remains repeatable and scalable, even as the software footprint grows.
Measuring success: patch coverage, MTTP, and continuous improvement
Evaluate the patch program with concrete metrics such as patch coverage and mean time to patch (MTTP). Regular measurement helps identify gaps and guide ongoing improvement in line with vulnerability remediation goals.
Continuous improvement ties patching outcomes to security objectives, emphasizing cybersecurity patching and vulnerability remediation. By documenting lessons learned and updating policies, small teams can sustain effective patch management through iterative enhancements and better risk management.
Frequently Asked Questions
What are patch management essentials for small teams and how can patch management for small teams implement them?
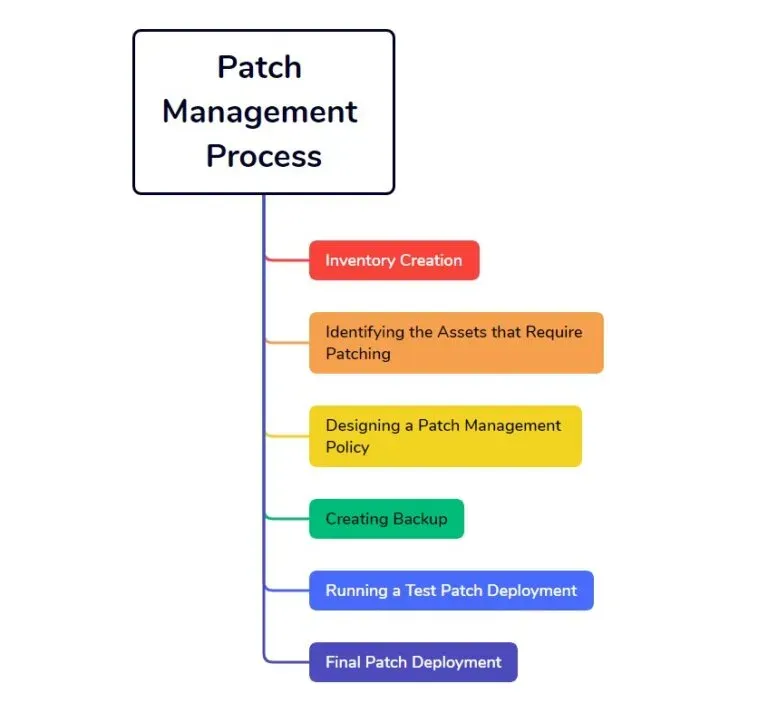
Patch management essentials are a repeatable process that covers asset discovery, patch identification, testing, deployment, verification, change control, and governance. For patch management for small teams, implement these steps with lightweight automation, a simple policy, phased deployments, and clear roles to minimize downtime while maintaining security. This approach also supports vulnerability remediation by ensuring timely, auditable patch actions.
How do patch management best practices influence software update management in a patch management for small teams context?
Patch management best practices guide you to prioritize by risk, test selectively, automate repetitive tasks, and document changes. When applied to software update management, they help ensure security-focused updates are deployed first while non-critical updates are scheduled without overwhelming the team. For small teams, align these practices with a practical cadence and governance to maintain effective patching.
Why is cybersecurity patching essential for vulnerability remediation within patch management essentials?
Cybersecurity patching is a core defense that reduces exposure to known weaknesses and limits attacker opportunities. In patch management essentials, vulnerability remediation goes beyond patches by incorporating assessments, threat intel, and timely fixes to identified gaps. Together, they create a proactive security posture for endpoints, servers, and cloud resources.
What are the essential steps in patch management for small teams to ensure effective patching?
Key steps include: 1) asset discovery and inventory; 2) patch identification and risk assessment; 3) testing and staging; 4) deployment planning and execution; 5) verification and reporting; 6) change control and rollback; 7) governance and continuous improvement. For small teams, keep the process lightweight, automate where feasible, and maintain clear documentation to support audits and ongoing improvement.
How does software update management relate to vulnerability remediation and cybersecurity patching in patch management essentials?
Software update management focuses on applying all updates, while vulnerability remediation prioritizes security-related patches to close exposed gaps. In patch management essentials, align your updates with a vulnerability-driven approach, ensuring critical security fixes are deployed promptly and non-critical updates are scheduled to minimize risk and disruption. This balance helps maintain security without overwhelming resources.
What role does automation play in patch management for small teams to improve cybersecurity patching?
Automation plays a central role by scanning for missing patches, orchestrating deployments, and generating compliance reports. For patch management for small teams, lightweight automation reduces manual effort, accelerates patch cycles, and preserves control through approvals, testing, and rollback safeguards, all of which strengthen cybersecurity patching and vulnerability remediation.
| Topic | Key Points |
|---|---|
| What Patch management essentials cover | Patch management essentials provide a repeatable process to discover devices, identify relevant patches, test as feasible, deploy updates, verify installation, and maintain audit trails, with considerations for exceptions, rollback, and stakeholder communication to minimize disruption. |
| Why small teams should invest | – Reduced attack surface by timely patches – Improved stability through tested updates – Compliance and governance through documented processes – Efficient use of scarce resources via automation and clear roles. |
| Core components | 1) Asset discovery and inventory 2) Patch identification and risk assessment 3) Testing and staging 4) Deployment planning and execution 5) Verification and reporting 6) Change control, rollback, and exception handling 7) Governance, policy, and continuous improvement |
| Building a practical, repeatable process | Step 1: Create a minimal but complete patch policy Step 2: Establish a cadence for patching Step 3: Instrument with lightweight automation Step 4: Communicate with stakeholders Step 5: Review and adapt |
| Patch management best practices | – Prioritize based on risk and critical systems – Test selectively but consistently – Automate where feasible – Maintain versioning and documentation – Align with security goals and policy requirements |
| Software update management vs patch management | Patch management emphasizes security fixes and remediation; software update management may include feature updates. Focus on prioritizing security-related updates first, then non-critical improvements as resources allow. |
| Cybersecurity patching & vulnerability remediation | Timely patching reduces exposure to weaknesses. Vulnerability remediation extends patching with assessments, configuration reviews, and threat intel to address gaps and strengthen endpoints, servers, and cloud resources. |
| Tools & automation to support essentials | – Endpoint inventory and discovery – Patch catalog and applicability checks – Testing and staging capabilities – Deployment scheduling and rollback options – Reporting and dashboards for compliance |
| Common challenges & practical solutions | – Limited IT staff/time: prioritize by risk and automate repetitive steps – Compatibility issues: staged deployments and rollback plans – Incomplete asset inventory: start with critical devices and expand – Insufficient reporting: define minimal KPIs and automate reports |
| Measuring success & continuous improvement | Track patch coverage, deployment success rate, MTTP, unpatched critical assets, and remediation progress. Regular reviews drive policy updates and process refinements for ongoing efficacy. |
| A practical, example workflow for small teams | – Monday: scan for missing patches – Tuesday: triage by severity; select patches for testing – Wednesday: test on a small group; monitor – Thursday: if testing passes, roll out in phases – Friday: verify installation and finalize reports |