Software patches are a core, but often underappreciated, pillar of any organization’s IT strategy. When people hear the word patch, they often think only of quick security updates. In reality, patches cover a broad spectrum: security patches that fix vulnerabilities, a vulnerability patch that addresses newly discovered weaknesses, bug patches that improve stability, compatibility patches that enable new hardware or software, and feature patches that add or refine capabilities. Understanding what patches do and how to manage software updates is essential for keeping systems secure, compliant, and performing at peak efficiency. This guide unlocks the mystery behind patches, explains why a disciplined patch management approach matters for patch deployment, and offers practical steps, practices, and pitfalls to avoid.
Viewed through alternative terms, the same concept centers on ongoing patching, update cadences, and vulnerability remediation across the IT estate. Organizations coordinate software maintenance, security fixes, and patch deployment across endpoints, servers, and cloud services to prevent gaps before they can be exploited. This broader view aligns with governance, asset management, and compliance checks, ensuring that risk-based decisions keep environments resilient as platforms evolve. By embracing language like patching, updates, fixes, and remediation, teams communicate more effectively with stakeholders, auditors, and security teams while maintaining strong protection.
1. Software patches and patch management: aligning updates with security and resilience
Software patches are more than quick security updates; they encompass security patches, bug fixes, compatibility patches, and feature patches. Understanding what patches do and how to manage updates is essential for keeping systems secure, compliant, and performing at peak efficiency. In this context, patch management combines software updates, vulnerability patch handling, and disciplined deployment practices to minimize risk while maximizing availability.
Effective patch management aligns patching activity with risk-based decision making. By treating software patches as strategic assets rather than routine chores, organizations can improve resilience, reduce exposure to cyber threats, and maintain regulatory compliance. The goal is a streamlined patch deployment process that supports security updates across endpoints, servers, and cloud services, while preserving user productivity and system stability.
2. Patch types and their impact on security, stability, and compatibility
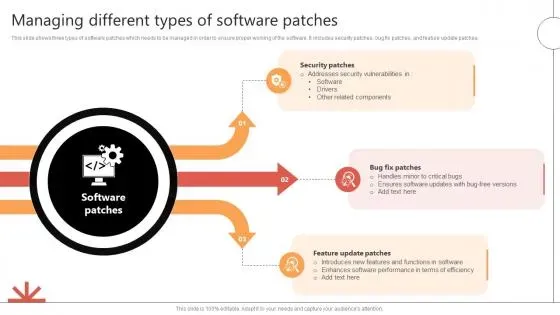
Patches come in several forms, each with its own impact profile on security and operations. Security patches and vulnerability patches address known weaknesses and CVEs, while bug fixes (quality patches) resolve defects that affect stability and data integrity. Compatibility patches ensure software runs smoothly on newer hardware, operating systems, and dependencies, and feature updates provide long-term value by adding enhancements.
Understanding these types helps IT teams prioritize work and communicate with stakeholders. A risk-based approach weighs the urgency of security updates against potential disruption from testing and deployment, guiding decisions about patch deployment cadences and maintenance windows. This balance is central to effective patch management and the ongoing health of the software stack.
3. The patch management lifecycle: discovery, assessment, testing, and deployment
A systematic patch management lifecycle reduces risk and accelerates deployment. It typically starts with discovery and inventory to map assets, versions, and exposure. Next comes assessment and prioritization, where release notes, CVSS scores, and business impact inform which patches take precedence, especially for internet-facing services and critical infrastructure.
The cycle continues with testing and validation in controlled environments, deployment planning with phased rollouts and maintenance windows, and deployment followed by verification. Rollback and remediation paths are prepared in advance, and thorough documentation supports audits and compliance. Regular review and improvement ensure the process evolves with changing threats, technologies, and organizational needs.
4. Testing, validation, and deployment strategies for reliable software updates
Robust testing and validation reduce the risk of disruption from software updates. A representative staging environment helps catch compatibility issues, performance regressions, and integration conflicts before production. Regression testing, end-to-end workflows, and security validation are essential parts of ensuring that patches do not degrade user experience.
Deployment strategies should balance speed with safety. Phased pilots on non-critical systems, maintenance-window deployments, and staggered rollout plans limit blast radii and simplify rollback if needed. Automated verification after deployment confirms successful installation and that security controls are intact, while post-deployment monitoring highlights any anomalies needing remediation.
5. Automation, tools, and integration for scalable patch deployment
Modern patch management relies on automation and integrated tooling to scale across endpoints, servers, and cloud workloads. Asset discovery, patch scanning, advisory ingestion, and test automation support faster, more reliable software updates. Centralized patch management tools enable consistent patch deployment, better reporting, and stronger control over patch deployment and patch deployment timelines.
Beyond on-premises systems, cloud-based patching, configuration management, and container/serverless patching expand coverage. The right mix of tools supports patch management, vulnerability management, and incident response, tying together software updates with governance, compliance, and risk monitoring. This integrated approach improves visibility into patch coverage and reduces manual error.
6. Measuring success: metrics, governance, and continuous improvement in patch management
Measuring patch management effectiveness requires clear metrics such as time to patch, patch coverage, success rates, and rollback frequency. Dashboards and audit trails provide visibility into patch deployments, approvals, and remediation actions, helping organizations demonstrate compliance with regulatory requirements. Tracking CVEs and vulnerability patches informs risk posture and prioritization decisions.
Continuous improvement comes from postmortems, performance reviews, and cross-functional collaboration between IT, security, and business units. Regularly analyzing failure modes, adjusting cadences, and updating governance practices ensure that patch management stays aligned with evolving threats, technology stacks, and organizational objectives. This disciplined approach makes software updates a resilient, measurable part of the security and operations program.
Frequently Asked Questions
What is patch management and why is it essential for software patches and security updates?
Patch management is the systematic process of identifying, testing, deploying, and validating software patches across an organization. It ties directly to software updates and security updates, ensuring vulnerabilities are remediated and systems stay compliant. A disciplined patch management program reduces risk, improves stability, and speeds safe patch deployment.
What are the main types of patches and how do vulnerability patches differ from security updates?
Patches fall into several types: security patches, vulnerability patches, bug fixes, compatibility patches, and feature updates. Vulnerability patches specifically address newly discovered weaknesses and are often tied to CVEs, while security updates remediate known vulnerabilities that could be exploited. Both require careful testing and timely patch deployment to minimize risk.
How should organizations plan patch deployment to minimize disruption and downtime?
Plan patch deployment by creating an asset inventory, testing patches in a staging environment, and using phased rollouts with maintenance windows. Define rollback plans and verification steps to confirm success after each phase, ensuring business continuity during software updates and patch deployment.
How do you prioritize patches in a patch management program, including vulnerability patch and security update considerations?
Prioritization uses risk-based criteria: critical security updates for internet-facing systems, high-CVSS patches, and patches for core services. Consider business impact, regulatory requirements, and the exposure level when planning patch deployment and applying vulnerability patches. This helps focus limited resources on patches that reduce the greatest risk.
What practices improve the effectiveness of software updates and patch deployment?
Adopt a repeatable process: maintain an up-to-date asset inventory, use centralized patch management tools, automate discovery and reporting, test patches in a representative environment, and schedule deployments with clear rollback options. Verify outcomes after each software update to ensure improvements are realized without disruption.
What common pitfalls should be avoided in vulnerability patches and patch management?
Avoid gaps in asset visibility, overreliance on automation without testing, and poor change control. Also watch for incompatible software stacks, insufficient rollback readiness, and compliance drift, all of which can undermine patch deployment and vulnerability patch remediation.
| Topic | Key Points |
|---|---|
| What Software Patches Do | Patches address gaps after code ships and serve three core purposes: 1) close security gaps to reduce risk; 2) fix defects to improve reliability; 3) enable compatibility and feature improvements. Patches may combine these purposes, and timely, well-coordinated deployment is a strategic risk-management activity. |
| Types of Patches | Security patches; Vulnerability patches; Bug fixes (quality patches); Compatibility patches; Feature updates (optional patches). Each type has its own risk and deployment considerations. |
| Patch Management Lifecycle | Discovery and inventory; Assessment and prioritization; Testing and validation; Deployment planning; Deployment and verification; Rollback and remediation; Documentation and compliance; Review and improvement. |
| How to Manage Updates Effectively | Build a complete asset inventory; Prioritize by risk; Test before deployment; Automate where possible; Schedule patches thoughtfully; Implement rollback plans; Verify outcomes; Document approvals and changes; Communicate with stakeholders. |
| Best Practices | Establish a defined cadence; Use centralized patch management tools; Emphasize security first but balance operations; Test in representative environments; Prioritize endpoint protection during patching; Maintain rollback capability; Monitor vendor advisories and CVEs; Align with governance and compliance. |
| Challenges and Pitfalls | Incomplete asset visibility; Overreliance on automation without testing; Poor change control; Incompatible software stacks; Insufficient rollback readiness; Compliance drift. |
| Security, Compliance, and Bigger Picture | Patches are a core component of security posture and regulatory compliance. Effective patching supports incident response, vulnerability management, asset management, and ongoing risk assessment by providing visibility into coverage and exposure. |
| Tools and Automation | Centralized update services, patch management solutions, test automation, staged deployments, rollback/remediation, and audit-ready reporting. Cloud, automation, and configuration management extend coverage to modern environments. |
| A Quick Case Example | A mid-sized organization uses an asset inventory, CVSS-based risk scoring, phased patch rollout, staging tests, and maintenance-window deployments to minimize disruption and improve auditability. |
Summary
Software patches are not just code updates; they are a strategic asset that protects systems, supports business continuity, and drives ongoing improvement. A well-structured patch management program combines a clear understanding of patch types, a rigorous lifecycle, automation where appropriate, and disciplined risk-based decision-making. By prioritizing critical security patches, validating changes in a staging environment, and maintaining clear documentation, organizations can keep their software patches effective, efficient, and aligned with business objectives. When patches are managed thoughtfully, they become a foundation for resilience, security, and long-term success in a complex technology landscape.