Patch management is a cornerstone of modern IT operations. Effective policy and governance support vulnerability remediation and ensure software updates and patches stay timely. A formal, repeatable patching program links discovery, testing, and deployment into an auditable lifecycle. Organizations can reduce risk by implementing consistent change controls, documented rollback plans, and clear deployment windows. This approach aligns with broader security goals and supports regulatory readiness without disrupting daily operations.
Viewed through an alternative lens, the same discipline can be described as a patching strategy, update governance, and lifecycle management for software. This focus supports vulnerability remediation, ensuring timely deployments across endpoints and reducing exposure to known flaws. It emphasizes discovery, testing, phased rollout, and rollback planning to minimize user disruption. Automated inventory, cross-platform coverage, and secure update channels help sustain an ongoing update program. In practice, clear governance and measurable metrics turn software updates and patches into a resilient, compliant operation.
Patch management: A strategic security backbone for modern IT environments
Patch management is a strategic security and operations practice that reduces the window of exposure from known vulnerabilities, helps keep applications compliant with industry standards, and ensures systems perform as intended. By treating patching as a repeatable, auditable cycle rather than a reactive task, organizations can align security with business goals and improve overall resilience.
A mature patch program starts with formal policy, accurate inventory, and ongoing improvement. Establishing clear roles, baselines, and a governance framework ensures that vulnerability remediation is prioritized, tracked, and integrated with broader security initiatives such as incident response and asset management.
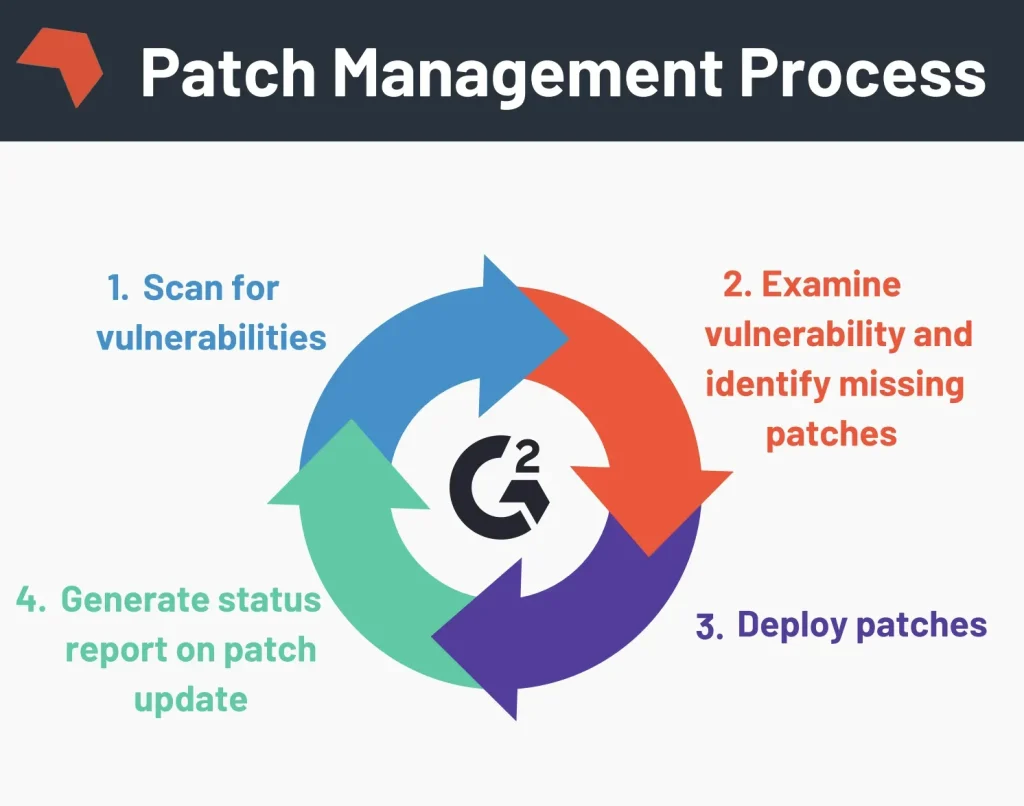
Understanding the Patch management process: A practical, repeatable cycle
A robust Patch management process begins with discovery and baseline creation to map hardware, operating systems, applications, and firmware. A reliable baseline defines what “current” looks like in your environment and highlights components that require attention.
The cycle continues with vulnerability assessment and risk prioritization, patch testing and staging, controlled deployment, verification, and reporting. Continuous improvement then feeds back into updated baselines and schedules to strengthen the overall program.
Endpoint patch management: Securing devices across Windows, macOS, Linux, and mobile
Endpoint patch management focuses on devices that connect to the network, including laptops, desktops, servers, mobile devices, and IoT endpoints. A comprehensive approach requires cross-platform coverage for Windows, macOS, Linux, and mobile operating systems, plus critical applications.
Organizations often balance agent-based and agentless approaches, choosing based on scale, security requirements, and network topology. Remote work and cloud-based update channels further influence how endpoints receive software updates and patches in a timely, auditable manner.
Software updates and patches: Distinguishing updates from security fixes and their deployment
Software updates and patches are related but distinct concepts. Patches typically fix vulnerabilities or bugs, while updates may introduce new features or performance improvements. A mature Patch management program treats both as valuable items that require timely assessment and deployment.
Governance should address prioritization, scheduling, and compatibility testing. A well-planned approach considers automatic deployment for low-risk patches and maintenance windows for higher-risk or feature-rich updates, always balancing security with user experience.
Vulnerability remediation through proactive patching and compliance
Patch management is a primary mechanism for vulnerability remediation. Timely patching reduces exposure to exploit kits and zero-day threats, supports regulatory compliance, and aids audits.
Preparing for zero-day incidents, automating reporting, and maintaining a defense-in-depth posture are essential. Integrating patch management with vulnerability management, incident response, and asset management strengthens overall security hygiene.
Measuring success with patch management best practices and key metrics
Effective patch management relies on best practices and meaningful metrics that drive improvement. Key indicators include patch compliance rate, mean time to patch (MTTP), and patch delay by severity, all tracked through regular dashboards.
Additional measures, such as coverage by platform and application, rollback readiness, and exceptions management, help governance bodies monitor progress. Continuous improvement, informed by these metrics, moves organizations toward a mature, risk-based Patch management program.
Frequently Asked Questions
What is patch management and how does the Patch management process reduce security risk?
Patch management is the process of acquiring, testing, and applying patches to fix vulnerabilities and improve stability. The Patch management process helps reduce exposure by prioritizing, validating, and deploying patches safely, turning reactive fixes into a repeatable, auditable cycle. It also supports vulnerability remediation by closing known gaps quickly and keeping systems compliant.
What are Patch management best practices for enterprise IT?
Core Patch management best practices include a formal policy, accurate software inventory, automation, risk-based prioritization, and standardized testing and phased deployment. Establish a patch management policy, automate scanning and deployment where possible, and plan maintenance windows with rollback options. Regular reporting and continuous improvement help maintain security and uptime.
What is Endpoint patch management and why is it important across devices and platforms?
Endpoint patch management focuses on devices that connect to your network—laptops, desktops, servers, mobile devices, and IoT. It should cover Windows, macOS, Linux, and critical applications, using both agent-based and agentless approaches as appropriate. A unified endpoint strategy reduces risk by ensuring timely patching across all endpoints, including remote devices.
How should Software updates and patches be managed as part of Patch management?
Software updates and patches are both part of a mature Patch management program. Distinguish security patches from feature updates, schedule deployments with testing, and govern changes through prioritization and change control.
How does Patch management contribute to vulnerability remediation and regulatory compliance?
Patch management is a primary mechanism for vulnerability remediation and regulatory compliance. Timely patching reduces exposure to threats and supports audit readiness through automated reports on patch status, compliance by asset class, and overdue patches.
What metrics should I track to measure Patch management effectiveness?
Key metrics include patch compliance rate, mean time to patch (MTTP), patch delay by severity, rollback readiness, and coverage by platform and application. Regular dashboards and KPIs help leadership track progress and drive ongoing improvements.
| Topic | Key Points |
|---|---|
| Patch management (Definition) | The process of acquiring, testing, and applying patches to software and operating systems to fix defects, close security gaps, and improve functionality. It aims to reduce risk, minimize disruption, keep applications compliant with standards, and ensure systems perform as intended. |
| Why Patch management matters | Keeps environments secure and stable by reducing exposure to known vulnerabilities, supporting regulatory compliance, and maintaining reliable, auditable IT operations. |
| The Patch Management Process: A Practical, Repeatable Cycle | 1) Inventory and baseline creation: catalog hardware, software, and firmware to establish a current baseline. 2) Vulnerability assessment and risk prioritization: rank patches by risk (e.g., CVSS, asset criticality, exposure). 3) Patch testing and staging: validate compatibility and detect issues in a controlled environment. 4) Deployment and change control: phased rollout with approval workflows and rollback plans. 5) Verification and reporting: confirm installation and system stability; produce compliance and risk reports. 6) Continuous improvement: update baselines and adjust schedules for zero-day responses. |
| Embracing Best Practices | Establish a formal policy; build a reliable software inventory; automate where possible; use risk-based prioritization; test patches before deployment; plan maintenance windows and rollback; integrate endpoint patch management with broader security; monitor, measure, and report using KPIs (e.g., patch compliance rate, MTTP). |
| Endpoint Patch Management: Across Devices and Platforms | Ensure cross-platform coverage (Windows, macOS, Linux, mobile); choose between agent-based or agentless approaches; address remote work with cloud-based catalogs and secure channels; include application patching and software updates in the lifecycle. |
| Software Updates vs. Patches | Patches fix specific vulnerabilities or bugs, while software updates may add features or broader changes. Both require prioritization, scheduling, and testing. Security patches typically take precedence over non-security updates. |
| Security, Compliance, and Vulnerability Remediation | Patch management is central to vulnerability remediation, regulatory compliance, and audit readiness. It includes zero-day readiness, automated reporting, and a defense-in-depth approach with other controls. |
| Tools, Metrics, and Maturity | Rely on patch management platforms that integrate with endpoint management, SIEM, and vulnerability scanners. Track KPIs like patch compliance rate, mean time to patch (MTTP), patch delay by severity, rollback readiness, and coverage by platform/application. |
| Common Challenges and Practical Solutions | Fragmented environments require centralized consoles and automation; limited visibility demands inventory and continuous monitoring; tests can bottleneck deployments, so standardize scripts and runbooks; manage user impact with clear communication and planned maintenance. |
| The Road Ahead | Automation, policy-driven governance, strong change control, and continuous improvement will keep patching effective as threats evolve, while preserving user productivity and service availability. |
Summary
Patch management is a foundational practice in modern IT operations, enabling organizations to reduce exposure to vulnerabilities, maintain compliance, and ensure system stability. A repeatable lifecycle—from inventory and risk-based prioritization to testing, deployment, verification, and continuous improvement—supports secure and resilient environments. Embracing best practices, robust endpoint patch management, and smart tooling helps organizations stay ahead of threats while minimizing disruption. The Road Ahead for patch management is through automation and governance that align security with business goals.