Software patch management for small businesses is not just about applying updates; it’s a strategic security practice that protects endpoints, servers, and customer data. For SMBs with small IT teams, patching can feel overwhelming, but a clear policy and repeatable workflows turn it into a reliable security program. By framing patching around patch management best practices, you can shorten remediation times and improve visibility for what needs attention across on-premises and cloud environments. The approach also supports small business cybersecurity by reducing attack surfaces and aligning patch deployment for SMBs with vulnerability management for SMBs. When you integrate patch deployment automation and centralized reporting, you gain predictable costs and smoother operations that keep patches current.
In other words, maintaining up-to-date software across a small enterprise requires an update governance strategy that spans devices, networks, and cloud services. Think of it as proactive vulnerability remediation and a structured patch cycle that reduces exposure without overloading IT teams. Consider terms like update management for SMBs, patching lifecycle, and security hygiene as related concepts that reinforce the same goal. LSI-friendly phrasing connects concepts such as patch rollout, automated discovery, risk-based prioritization, and compliance readiness to the core practice.
Software patch management for small businesses: foundations, goals, and practical scope
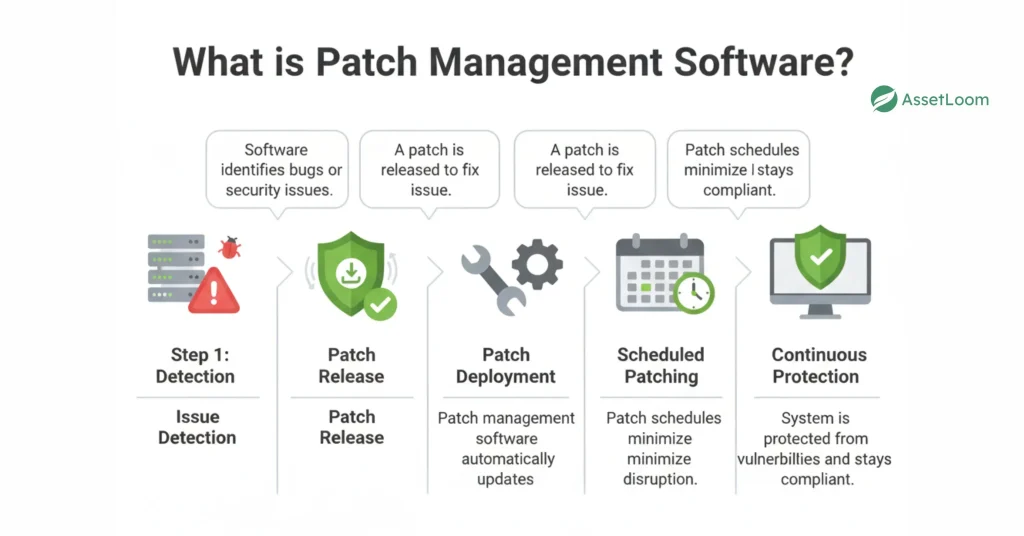
Software patch management for small businesses is a structured security practice that covers the end-to-end lifecycle of updates—from identifying available patches to verifying successful installation. For SMBs, this means focusing on endpoints, servers, and even firmware across laptops, printers, and network gear, while keeping the process accessible to lean IT teams. The goal is to turn patching from ad hoc updates into a repeatable security program that reduces risk and aligns with patch management best practices. By adopting a practical scope and clear policy, small businesses can improve security hygiene without overwhelming resources.
This foundation sets expectations for how patch management contributes to broader small business cybersecurity goals. It emphasizes predictable costs, measurable remediation times, and consistent reporting that supports audits and vendor risk management. With a well-defined scope, teams can balance speed and safety, ensuring critical systems stay protected while non-critical assets are patched on a sustainable cadence. The result is a security program that integrates smoothly into everyday operations.
Why patch management matters for SMBs in the context of cybersecurity
Small businesses are frequent targets because attackers assume fewer security controls and slower patch cycles. A robust patch management program reduces the attack surface by applying the latest fixes to critical vulnerabilities before they can be exploited. This emphasis on timely patches is a core component of small business cybersecurity, helping to protect customer data and maintain trust.
Beyond immediate risk reduction, patch management supports regulatory requirements and vendor risk management across industries such as healthcare, finance, and professional services. A well-executed program provides clear visibility into what’s in the environment, which patches remain outstanding, and how quickly critical issues are resolved. This transparency also strengthens vulnerability management for SMBs by linking patch activity to ongoing assessments and remediation efforts.
Core components of an SMB patch management program
A practical SMB patch management program starts with asset inventory and discovery: knowing what hardware and software you own, where they run, and how they connect. Without an accurate inventory, patch prioritization and deployment become guesswork, undermining the effectiveness of patch management for SMBs. The next steps—patch identification and risk assessment, testing and staging, deployment and scheduling, and verification—form a cohesive workflow that keeps patches flowing with minimal disruption.
Change control and reporting are essential to sustaining momentum. Aligning patch activities with formal processes enables better communication with stakeholders and supports compliance reporting. Regular verification, monitoring, and documentation of patch status create auditable trails that demonstrate due diligence during audits and vendor reviews, reinforcing the overall patch management best practices that SMBs strive to follow.
Automation and tools to accelerate patch deployment for SMBs
Automation is the lifeline of efficient patch management for small businesses. Seek affordable, easy-to-use patch management solutions that support multiple platforms (Windows, macOS, Linux), mobile devices, and network gear. Prioritize features such as centralized patch catalogs, automatic detection of missing patches, testing sandboxes, and integrated reporting. Patch deployment automation helps SMBs push patches across devices consistently, reducing manual effort and human error.
When selecting tools, consider whether the solution offers a lightweight, scalable approach that fits limited IT resources. Cloud-based or hybrid options can provide rapid deployment across on-premises and remote workers, while integration with vulnerability scanning and change management can enhance overall security governance. A well-chosen toolset enables ongoing improvement of patching workflows without introducing excessive complexity.
Practical deployment strategies for SMBs: phased rollout and risk management
Patch deployment for SMBs should begin with critical systems—email servers, file servers, ERP/CRM platforms, and internet-facing services—where exploitation would cause the greatest impact. Implement maintenance windows during off-peak hours to minimize business disruption, and use a phased rollout approach: pilot a small group, monitor for issues, then expand in waves.
A clear rollback plan is essential. Ensure backups exist and that you can revert patches if needed. Build fallback options for incompatible environments, such as firewall mitigations or application-level workarounds, to keep operations running while patches are staged. This structured approach aligns with patch management best practices and supports a steady, low-risk path to broader deployment.
Continuous improvement: integrating vulnerability management for SMBs with patching practices
Patch management is an ongoing discipline that should complement vulnerability scanning and remediation workflows. Regular vulnerability assessments help identify gaps and verify that remediation efforts are effective, ensuring that patch activities translate into tangible risk reduction. Documenting patch cycles, testing evidence, deployment windows, and completion status supports compliance checks and vendor requirements.
A disciplined, iterative mindset enables continuous improvement: refine prioritization rules, expand automation, and adapt processes to changing environments and threats. By viewing patching as a core element of vulnerability management for SMBs, you can maintain visibility, measure impact, and demonstrate progress toward stronger security hygiene over time.
Frequently Asked Questions
How does software patch management for small businesses reduce risk and improve security?
Software patch management for small businesses reduces risk by systematically identifying, testing, and deploying patches to critical assets. It closes known vulnerabilities, shortens remediation times, and improves overall security hygiene. Following patch management best practices helps SMBs maintain visibility and control even with limited IT resources.
What are the core components of patch management for small businesses?
Core components include asset inventory and discovery, patch identification and risk assessment, testing and staging, deployment and scheduling, verification and reporting, and change control. Using patch deployment automation and centralized tooling helps SMBs execute these steps consistently across devices.
How should a small business prioritize patches in patch management for small businesses when resources are limited?
In patch management for small businesses, prioritize by risk: focus on critical vulnerabilities, those publicly exploited, and assets essential to operations. Establish a formal policy, use risk scoring, test patches on a representative group, and deploy in phased rollouts to minimize disruption.
What role does patch deployment automation play in software patch management for small businesses?
Patch deployment automation accelerates patch delivery, reduces manual effort, and minimizes human error across Windows, macOS, Linux, and network gear. It enables centralized patch catalogs, automatic detection of missing patches, testing sandboxes, and integrated reporting—key benefits for software patch management for small businesses.
What would a practical 30-day quick-start plan look like for patch management for small businesses?
A practical 30-day plan: Day 1–7 inventory and policy; Day 8–14 prioritization and testing; Day 15–21 pilot deployment; Day 22–30 full rollout and review. This approach aligns with patch management for small businesses and leverages patch deployment automation where possible.
How does patch management tie into vulnerability management for SMBs and compliance within software patch management for small businesses?
Patch management supports vulnerability management for SMBs by closing gaps identified by vulnerability scanning and providing audit trails for compliance reviews. Regular patching, testing, and reporting help meet regulatory requirements and vendor expectations. Integrating these activities into patch management for small businesses enables continuous improvement.
| Topic | Key Points |
|---|---|
| Introduction | Patch management is a strategic security practice that protects endpoints, servers, and customer data. For SMBs with small IT teams, assets are spread across on‑premises devices, cloud workspaces, and employee devices. Delays create exploitable gaps. This quick guide provides practical steps to build a reliable workflow, reduce risk, improve security hygiene, and keep costs predictable while shortening remediation times and increasing visibility. |
| What is software patch management for small businesses? | End-to-end lifecycle: identifying patches, evaluating risk, testing to prevent disruption, deploying, and verifying patches. Covers OS, third‑party software, and firmware on devices like laptops and servers. SMBs focus on critical assets, fast remediation, and repeatable workflows; policy and routine turn patching into a measurable security program. |
| Why patch management matters for SMBs | Attackers target SMBs due to fewer controls and slower patch cycles. A strong patch program reduces the attack surface and supports regulatory compliance in industries like healthcare, finance, and professional services. Benefits include fewer incidents, lower downtime, and improved customer trust; better visibility into what’s in the environment and which patches are outstanding. |
| Core components of an SMB patch management program | – Asset inventory and discovery: know hardware/software, where it runs, and how connected. Without inventory you can’t patch effectively. – Patch identification and risk assessment: track vendor advisories, assess exploitability, prioritize by impact and exposure. – Testing and staging: test patches on a subset to reduce compatibility issues. – Deployment and scheduling: standard maintenance windows, automated deployment where possible, staged rollouts. – Verification and reporting: confirm installation and maintain audit trails. – Change control and awareness: align with change management and communicate with stakeholders. |
| Key best practices for patch management in small businesses | – Establish a formal patch policy with roles, timelines, and approvals – Prioritize patches by risk for critical vulnerabilities – Automate where feasible to speed delivery and reduce errors – Test patches before broad deployment – Use phased deployment (pilot → larger groups → full rollout) – Verify installation and monitor status – Maintain a vulnerability-management mindset – Plan for rollback and remediation – Align with compliance and reporting |
| Automation, tools, and process design for SMBs | Automation is essential for efficiency. Choose affordable, easy-to-use patch management solutions that support multiple platforms and devices. Look for centralized patch catalogs, automatic detection of missing patches, testing sandboxes, and integrated reporting. A lightweight solution that covers deployment across endpoints and servers can deliver substantial security benefits without heavy implementation. |
| Practical deployment strategies for SMBs | – Start with critical systems (email/file servers, ERP/CRM, internet-facing services) – Schedule maintenance windows during off-peak hours – Use phased rollout (pilot 5–10% of devices, then expand) – Define a rollback plan and ensure backups – Provide fallback options for incompatible environments (e.g., firewall rules, app-level mitigations) |
| Security, compliance, and continuous improvement | Ongoing risk reduction and governance. Regular vulnerability scanning complements patching. Document patch activities, testing evidence, deployment windows, and completion status for audits. Continuously improve by refining prioritization, expanding automation, and adjusting processes as environments evolve. |
| Common SMB challenges and how to overcome them | – Limited IT staff: use turnkey patch tools with guided workflows; consider managed services that include patching – Budget constraints: start small, demonstrate ROI via reduced incidents – Heterogeneous environments: prioritize critical platforms and use automation – Patch fatigue: centralize alerts, filter by risk, schedule reviews |
| A practical 30-day quick-start plan for SMBs | – Days 1–7: Inventory and policy — build asset inventory, draft patch policy, establish maintenance windows and reporting – Days 8–14: Prioritization and testing — set severity levels, create a sandbox, validate patches – Days 15–21: Pilot deployment — push high-priority patches to pilot group, monitor and adjust – Days 22–30: Full rollout and review — expand deployment, document outcomes, update policy, start ongoing vulnerability scans |
Summary
Conclusion: Software patch management for small businesses is an essential, ongoing security discipline. By adopting best practices, automating deployment where possible, and aligning patch activities with vulnerability management, SMBs can dramatically reduce risk without overburdening their teams. Start with a clear policy, implement automation, and use a phased rollout to protect critical systems. With a structured, continuous-improvement approach, a small business can stay ahead of threats, protect customer data, and maintain compliance—one patch at a time.