Software patches are essential updates that fix bugs, close security holes, and keep systems running smoothly, and this steady cadence enables teams to align patches with strategic objectives, budgets, and user expectations. To make those updates effective, organizations rely on patch management to orchestrate discovery, testing, deployment, rollback plans, and ongoing monitoring across devices, applications, and operating systems in complex environments, while centralizing resources, standardizing testing environments, and maintaining an authoritative software catalog. Prioritizing timely releases and validating compatibility helps minimize downtime while maximizing the security benefits of each release, and it supports redundancy planning, service-level objectives, and user-acceptance testing, while documenting decisions to support audit readiness and provide accountability for changes. Adopting a structured patching approach aligns with business goals, reduces the window of exposure, and supports compliance with industry standards such as regulatory frameworks, vendor guidance, and internal risk appetite, and adding review cycles that incorporate feedback from security teams and operations, which are reviewed quarterly with stakeholders. By treating updates as a repeatable, documented process, organizations can establish reliable routines that protect data, sustain operations during migrations, and adapt to evolving threats and changing technology stacks, with the goal of capturing lessons learned and refining required controls for continuous improvement and measurable outcomes.
Beyond the name itself, these updates are best understood as vendor-issued fixes and maintenance releases that address vulnerabilities, improve stability, and ensure software continues to function as intended. A disciplined approach to software maintenance treats these fixes as a formal process—identifying, testing, and deploying updates with controlled change management and clear rollback options. By framing patching as ongoing risk reduction rather than a one-off event, organizations align technical changes with governance, compliance, and business continuity objectives. In practice, this means integrating regular vulnerability checks, compatibility testing, backup strategies, and change-control procedures into the daily workflow so teams can act quickly and confidently.
1) What Software Patches Are and Why Patch Management Matters
Software patches are updates released by software vendors to fix defects, close security vulnerabilities, and sometimes enhance performance. They are the essential components of ongoing maintenance that keep systems resilient against evolving threats. Understanding software patches helps you see how even small updates can dramatically improve security, stability, and compatibility across your devices and applications.
Patch management is the deliberate, repeatable process of identifying, testing, deploying, and monitoring these updates across an organization. By reducing the window of opportunity for attackers and ensuring patches do not disrupt critical operations, patch management becomes a foundational security practice that aligns with broader risk management goals and business continuity.
2) From Vendor Patches to Production: How Patches Work in Practice
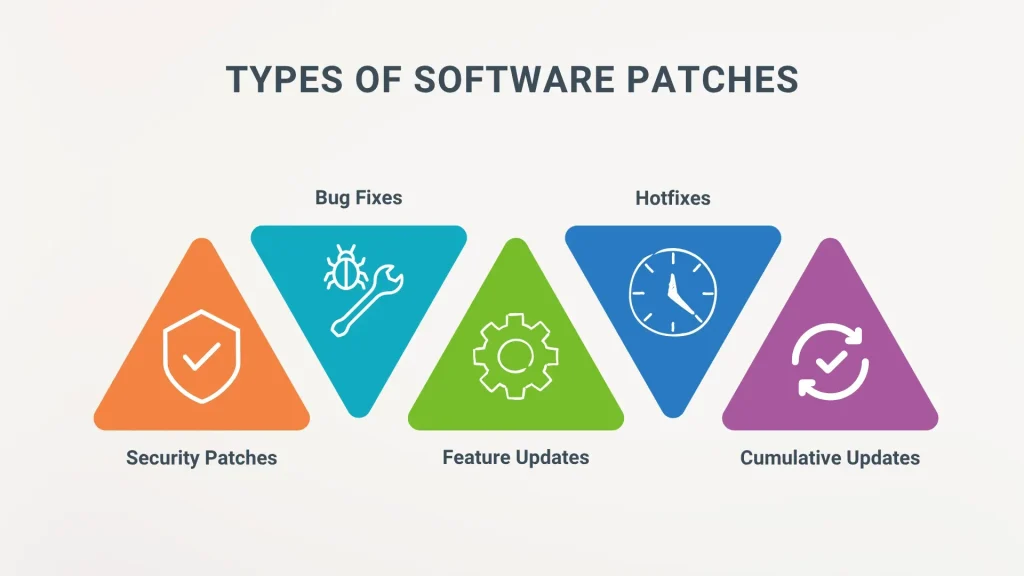
Patches originate with software vendors and are delivered through operating system update channels, enterprise management tools, or vendor portals. They can target security patches that fix vulnerabilities or non-security patches that address bugs, performance issues, or compatibility concerns. In many updates you’ll see a mix of improvements, which is why understanding the patch source and its impact is crucial for effective patch management.
Effective implementation requires testing and validation in environments that resemble production. This helps ensure patches do not break critical workflows, integrations, or security controls. A well-designed process includes staging, compatibility checks, and automated regression testing to verify that patches deliver the intended benefits without introducing new issues.
3) Prioritizing Patches: Aligning With Critical Patch Updates and Risk
Prioritization should be based on the severity of vulnerabilities, exposure of systems, and the criticality of the software to business operations. A common approach uses high, medium, and low risk categories, with high-risk or critical patch updates treated as urgent. This risk-based prioritization sharpens focus on the patches that minimize the greatest potential harm.
In tandem with prioritization, vulnerability remediation efforts should drive the patching cadence. Regular vulnerability scanning, asset discovery, and change monitoring help you know where gaps exist and when a patch will yield the most security benefit. The goal is to reduce exposure quickly while preserving system stability.
4) Deployment Strategies for Patch Management: Minimizing Downtime and Maximizing Security
A smart deployment strategy uses phased rollouts, starting with non-critical systems and expanding to mission-critical devices. This approach helps identify issues early and limits the blast radius of any patch-related problems. Integrate maintenance windows, reliable backups, and rollback plans to keep business operations uninterrupted.
As environments grow, automation and centralized patching tools become essential. Techniques such as scheduled updates, package manager workflows (apt, yum), and configuration management systems accelerate deployment while maintaining visibility and compliance. Following software patching best practices ensures consistency, traceability, and clear reporting across diverse devices and platforms.
5) Security Patches vs Feature Patches: Clear Priorities for Safe Patching
Security patches address vulnerabilities that could be exploited to compromise confidentiality, integrity, or availability. They typically require swift action to close attack surfaces and protect sensitive data. While feature patches can bring improvements, they are generally less urgent and should be scheduled after security patches are in place.
A mature patch program distinguishes these two types and emphasizes rapid deployment of security patches while testing feature updates for compatibility. Bundled updates that include both security fixes and feature improvements should be treated with the same level of due diligence, ensuring comprehensive validation before rollout.
6) Measuring Success and Avoiding Common Pitfalls in Patch Management
Success in patch management is measured by patch coverage, time to patch, and reductions in detected vulnerabilities. Tracking these metrics requires continuous vulnerability scanning, change tracking, and regular audits to verify that security patches are applied across the environment.
Common pitfalls include patch fatigue, compatibility issues with legacy systems, and rushed deployments. Mitigate these risks with automation, a clear rollback plan, and ongoing communication with stakeholders. By embedding vulnerability remediation into a disciplined workflow and maintaining a reliable baseline, you can sustain strong security while keeping systems productive.
Frequently Asked Questions
What are software patches and why is patch management crucial for vulnerability remediation and security?
Software patches are updates from vendors that fix defects and close security vulnerabilities. Patch management is the ongoing process of identifying, testing, deploying, and monitoring these patches to reduce exposure, accelerate vulnerability remediation, and strengthen security while maintaining stability.
What is a critical patch update and why should it be prioritized in vulnerability remediation?
A critical patch update addresses widely exploited vulnerabilities or those with severe impact. In patch management, prioritize these updates to reduce risk quickly, then test for compatibility to support vulnerability remediation and avoid downtime.
What are software patching best practices to maximize security and minimize downtime?
Follow software patching best practices: maintain an up-to-date inventory, classify patches by risk, test in a staging environment, deploy in phased rollouts, schedule maintenance windows, and verify backups before applying patches.
How can you measure the success of your patch management program when applying software patches?
Use metrics such as patch coverage (percentage of devices on the latest patches), time to patch (disclosure to deployment), and reductions in detected vulnerabilities, supported by continuous vulnerability scanning and change tracking.
What deployment strategies work best for security patches across large environments?
Adopt phased rollouts (start with non-critical systems), use centralized management tools, automate where possible, and ensure comprehensive reporting and backups; tailor schedules to minimize disruption while maintaining security.
What common pitfalls should organizations avoid with software patches and how can a policy help?
Common pitfalls include patch fatigue, compatibility issues, and testing delays. A clear patch policy—defining timing, testing, approvals, rollback steps, and responsible roles—helps reduce risk and improve consistency in patch management.
| Topic | Key Points | Impact / Benefits |
|---|---|---|
| What patches are and why they matter | Patches are vendor updates that fix defects, close security vulnerabilities, and sometimes improve performance. Patch management reduces the window of exposure and helps protect data and operations. | Improved security, stability, and reliability; lower risk of breaches. |
| How patches work in practice | Delivered by vendors via OS, management tools, or portals. Patches can be security or non-security patches; critical patch updates address widely exploited flaws. | Timely fixes and compatibility improvements across environments. |
| The risk they address | Delays leave systems vulnerable; patching too hastily can cause instability. Patch management balances risk reduction with stability and change control. | Reduced breach risk; maintained system reliability. |
| Patch management best practices (visibility & prioritization) | Maintain an up-to-date inventory; assess risk; define a policy for when/how patches are applied and who approves. | Clear governance and efficient prioritization of critical fixes. |
| Testing and validation | Test in staging; check compatibility with apps/drivers/configs; automate regression tests; plan workarounds or delays if issues arise. | Lower risk of production disruption; smoother rollout. |
| Deployment strategies | Phased rollout, maintenance windows, backups, and centralized tools; monitor after deployment; use OS/package managers for automation. | Minimized downtime; safer, auditable deployments. |
| Security vs feature patches | Security patches fix vulnerabilities; feature patches add improvements and may wait; treat bundles with caution and test thoroughly. | Prioritized security, controlled feature updates. |
| Measuring success and pitfalls | Metrics like patch coverage and time-to-patch; vulnerability scans and audits; watch for patch fatigue and compatibility issues. | Objective visibility into patch program effectiveness; reduces unintended downtime. |
| Putting patch management into practice | Baseline inventory and policy; vulnerability scanning; staging; rollback steps; extend to apps/cloud over time. | Progressive maturity and stronger security posture. |